DNS Hijack: Hazy Hawk Hit 34 Universities Including Berkeley
Hazy Hawk exploited forgotten DNS records to hijack 34+ universities including Berkeley and Columbia. Scam pages now rank on Google under .edu domains —...
Imagine Googling your alma mater's research center and landing on a page selling counterfeit pharmaceuticals — hosted under the university's official domain. That scenario is real for thousands of visitors right now at 34 confirmed universities, including UC Berkeley, Columbia, and Washington University. A threat group called Hazy Hawk has executed a large-scale DNS hijacking campaign — quietly seizing their subdomains via subdomain takeover, with Google Search indexing all of it.
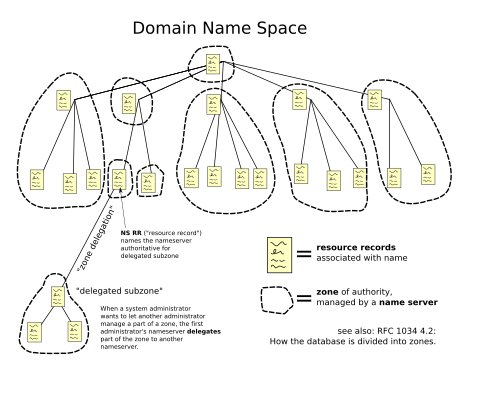
The method isn't a sophisticated zero-day exploit. It's a $10 domain registration — exploiting DNS records (the internet's address-book entries that map domain names to servers) that IT departments created years ago and never deleted.
How DNS Hijacking Works: A Forgotten Entry Hands Over Your Subdomain for $10
When a university department launches a project — a research portal, a conference site, a student-services tool — they typically create a subdomain (a web address like careers.university.edu or events.columbia.edu) and point it to an external hosting platform using a CNAME record (a DNS entry that redirects one domain name to another — like mail forwarding that stays active even after you've moved out). Common targets: AWS S3 buckets, GitHub Pages, Heroku apps, Netlify deployments.
When the project ends, the external hosting account gets cancelled. But the CNAME record pointing to it stays in the university's DNS configuration — unreviewed, unmonitored, sometimes for a decade or more.
Hazy Hawk's playbook exploits this gap systematically:
- Scan .edu domains for CNAME records pointing to expired or abandoned external services
- Register the abandoned target domain for as little as $10 per year
- Control exactly what gets served at the hijacked university subdomain
- Rank — because Google trusts .edu addresses, the hijacked pages immediately climb search results
The result: scam pharmaceutical stores, adult content, and malware downloads appearing to originate from Berkeley, Columbia, and 32 other top academic institutions. Google has indexed thousands of these pages across the confirmed affected universities — with no quick fix available once a page is in Google's index.

The Search Engine Angle: Why .edu Is the Perfect Attack Multiplier
Google's domain authority system (a measure of how much a website's historical reputation boosts its search ranking) gives .edu domains significant built-in credibility. Academic institutions have published peer-reviewed research, official announcements, and verified data for decades — so Google's algorithm has learned to rank .edu content highly by default.
Hazy Hawk inherits that accumulated trust instantly. The economics are stark:
- Attacker cost: $10–$50 per target domain registration
- Attacker gain: Decades of institutional credibility, immediate first-page Google placement
- University remediation cost: DNS record deletion takes minutes; Google deindexing takes days to weeks per URL
- Exposure window: Every Google Search session until each URL is individually deindexed
A fake pharmacy page on a random domain might rank on page 10. The same page hosted at research.columbia.edu appears on page one. Researchers confirmed that thousands of hijacked pages are currently indexed across 34+ institutions — and the confirmed universities are likely a fraction of the full scope. The campaign ran long enough for extensive Google indexing to occur before detection.
Why DNS Subdomain Takeover Keeps Happening: No One Owns the Cleanup
This isn't a software bug — no patch will fix it. It's an organizational failure: the absence of subdomain lifecycle management (a formal process tracking which subdomains exist, what external services they point to, and whether those services remain active and controlled by the institution).
University IT environments are structurally prone to this kind of accumulated neglect:
- Decentralized administration — individual departments create web properties without central IT oversight or approval
- Staff turnover — the person who created
conference2019.university.edugraduated, retired, or moved on years ago - No expiration mechanism — DNS records persist indefinitely unless manually deleted; there's no automatic cleanup when a pointed-to service goes offline
- Cloud platform proliferation — modern universities use dozens of SaaS tools (AWS, GitHub Pages, Netlify, Heroku, Azure) that each create potential orphaned CNAME targets when discontinued
- No gap-detection alerts — standard DNS management tools don't notify administrators when a CNAME target domain becomes unregistered and available to anyone with $10
Research universities with 30 to 100+ years of web history carry the most risk. Every abandoned research portal, conference site, student organization page, and departmental tool is a potential Hazy Hawk entry point. The 34 confirmed institutions represent only the documented cases — the group has been operating quietly across a larger surface.
A Week of Cascading Cybersecurity and Infrastructure Failures
The Hazy Hawk disclosures landed during a brutal week for infrastructure security. Two other major incidents compounded the picture in the same 48-hour window:
Ubuntu offline for 24+ hours: Canonical (the company maintaining Ubuntu Linux) lost its entire web infrastructure to a sustained DDoS attack (a distributed denial-of-service attack — flooding servers with artificial traffic until they become unreachable to real users) launched by a pro-Iran group using the Beam stressor service. The attack came immediately after a botched vulnerability disclosure, suggesting deliberate coordination.
CopyFail (CVE-2026-31431): Researchers disclosed the most severe Linux privilege escalation flaw in years. Its defining characteristic: a single working exploit payload operates across all Linux distributions without modification — previous privilege escalation flaws required custom payloads per distribution. Eight kernel versions received patches (7.0, 6.19.12, 6.18.12, 6.12.85, 6.6.137, 6.1.170, 5.15.204, 5.10.254), but most distributions had not deployed fixes before the public exploit became available. CopyFail additionally enables container escape (breaking out of isolated Docker or Kubernetes environments) and malicious injection into CI/CD pipelines (the automated systems that build and deploy software) — catastrophic vectors for cloud infrastructure at scale.
The pattern across all three incidents: public disclosure and active exploitation compounding before defenders can deploy fixes, leaving organizations scrambling simultaneously on multiple fronts.
How to Find and Fix DNS Subdomain Hijacking Exposure Right Now
The Hazy Hawk campaign is ongoing. Here's what each audience can do immediately, without waiting for a vendor patch or security advisory:
IT administrators and DevOps teams:
- Export all CNAME records from your DNS management console (Route 53, Cloudflare, GoDaddy, or your registrar's dashboard)
- For each record, verify the target domain is still registered and controlled by your organization or an active current vendor
- Prioritize records pointing to known abandonment-risk platforms: AWS S3, GitHub Pages, Netlify, Heroku, Azure Static Sites, Fastly
- Delete any CNAME pointing to an expired or uncontrolled target domain immediately — this takes under 60 seconds and eliminates the attack surface
- Implement a subdomain registry: a live document tracking every subdomain, its owner, its purpose, and its decommission date
Students, alumni, and general web users:
- If a .edu Google Search result serves unexpected content — pills, adult content, unfamiliar language — leave immediately and use Google's "Report" feedback option to accelerate deindexing
- Verify the full subdomain URL before entering any credentials;
login.university.eduandoldlogin.university.educarry very different security guarantees - Report suspicious university subdomains to the institution's IT security team directly — most have a
security@university.eduaddress
You can automate subdomain monitoring and DNS audits using AI-assisted security workflows — explore the security automation guides at aiforautomation.io. Tools for scanning dangling CNAME records exist and take under an hour to deploy. The question is whether your organization runs one before Hazy Hawk finds your forgotten records first. Get started with automated DNS monitoring here.
Related Content — Get Started | Guides | More News
Sources
Stay updated on AI news
Simple explanations of the latest AI developments